Cloud Identity and Access Management (IAM)
Managing users, their privileges and usage of the cloud in a dynamic multi- cloud environment can be a daunting task. Mitigate the risks associated with compromised credentials and insider threats by secure and timely management of identities and their access in the cloud.
Use Cases / Cloud IAM
Cloud Identity and Access Management (IAM)
Managing users, their privileges and usage of the cloud in a dynamic multi- cloud environment can be a daunting task. Mitigate the risks associated with compromised credentials and insider threats by secure and timely management of identities and their access in the cloud.
Automate resource permission management and ensure usage based access

Overview
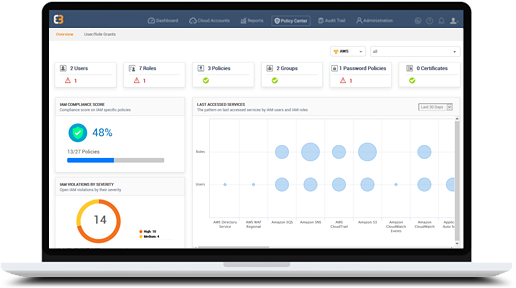
C3M Cloud Control combines identity and access management with cloud security and makes it easier to manage identity, user access, privilege and the risk of a trusted identity with excess privilege.

Overview
C3M Cloud Control combines identity and access management with cloud security and makes it easier to manage identity, user access, privilege and the risk of a trusted identity with excess privilege.
Gain Cloud Identity and Access Management Control
The platform helps you ascertain
What identities have access to cloud resources?
Whether any identities are over-provisioned?
Are any identities violating cloud best practices?
What are the recent IAM changes in the cloud account?
Who are the privileged users and do they use such privileges?
Complete Cloud Identity and Access Management Control
C3M Cloud Control enables the security teams to gain granular control and identify all active users and identities; monitor their activities; and avoid over-provisioned privileges.

Gain complete visibility into the users, identities and their privileges.
Monitor the users, identities, their actions, and its impact.
Regularize the excess privileges depending on the usage and business needs.
